...
| API | Proxy | |
|---|---|---|
Real Time (DLP and Ethical Wall) | X (will delete content within seconds) | V (will block communication from reaching the cloud) |
| Ethical Wall | ||
| Block Search | X | V |
| Chat | V | V |
| Files | V | V |
| Audio | X | V |
| Video | X | V |
| Screen share | X | V |
| Remove users from Teams/Chat | V | X There is no need to do this with the proxy approach since all communication can be blocked at source |
| Block remote control in meeting | X | V |
| Block user from being Guest in external tenant | X | V |
| eDiscovery | ||
| Chat messages and files | V | X |
| Meeting events | X | V |
| Screen share events | X | V |
eDiscovery using Proxy and API components
...
Deployment can support having both Proxy and API components.
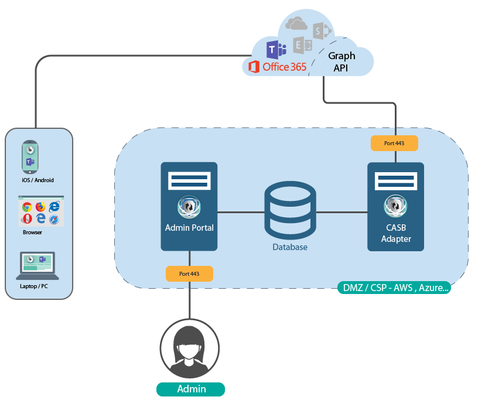
Adapter API Topology
This topology is the most simple to implement and is recommended to start with.
...
It does require use of ADFS or another IDP IdP in order to redirect the traffic to the SphereShield Reverse Proxy.
...